The purpose of the /etc/networks file
This article has last been updated at .
Also wondering what particular files do on Linux? One of those files we recently rediscovered during auditing is the /etc/networks file. For some reason it was always there, yet we never change it.

Output of /etc/networks
When looking at the man page of networks(5) we learn its purpose (almost instantly):
- It translates between IP ranges and network names
- It is used for tools like netstat and route
- It only works on class A, B, or C networks
- It does not work on subnets
Surprisingly enough a test with subnetting actually showed the right names during our test. Digging through the related system calls (getnetbyaddr(3), getnetbyname(3), getnetent(3)), it did not reveal the reason why it worked.
Query the networks database
Linux systems use different databases which can be queried with the getent utility. It is the abbreviated name for “get entries” and uses the Nameserver Switch Services libraries. You may have been a package like libnss installed on your system. You can consider them wrappers around files and data structures, like the /etc/networks file.
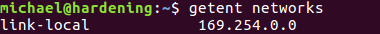
Querying the networks database is simple:
getent networks
Depending on your network configuration it may be more populated than our test system, which shows only one network. In this case just the “link-local” network (169.254.0.0), which is a reserved local network range for when no DHCP server is available. The system may then fall back on this range, to have at least some network.
A lonely network
Conclusion
The /etc/networks file has a limited purpose. It may help in displaying network names for some network related utilities. For more advanced network setups if may be useful to quickly show what network range belongs to which customer. We can conclude the /etc/networks file will not have a huge impact on how the system works.
Did you configure your /etc/networks file, or use it in a particularly useful way? Let it know!

